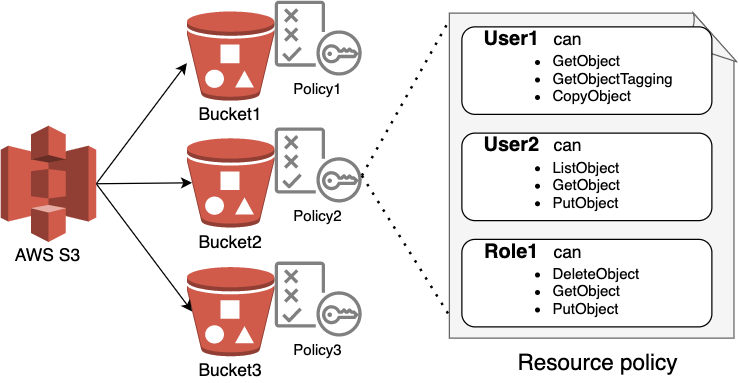
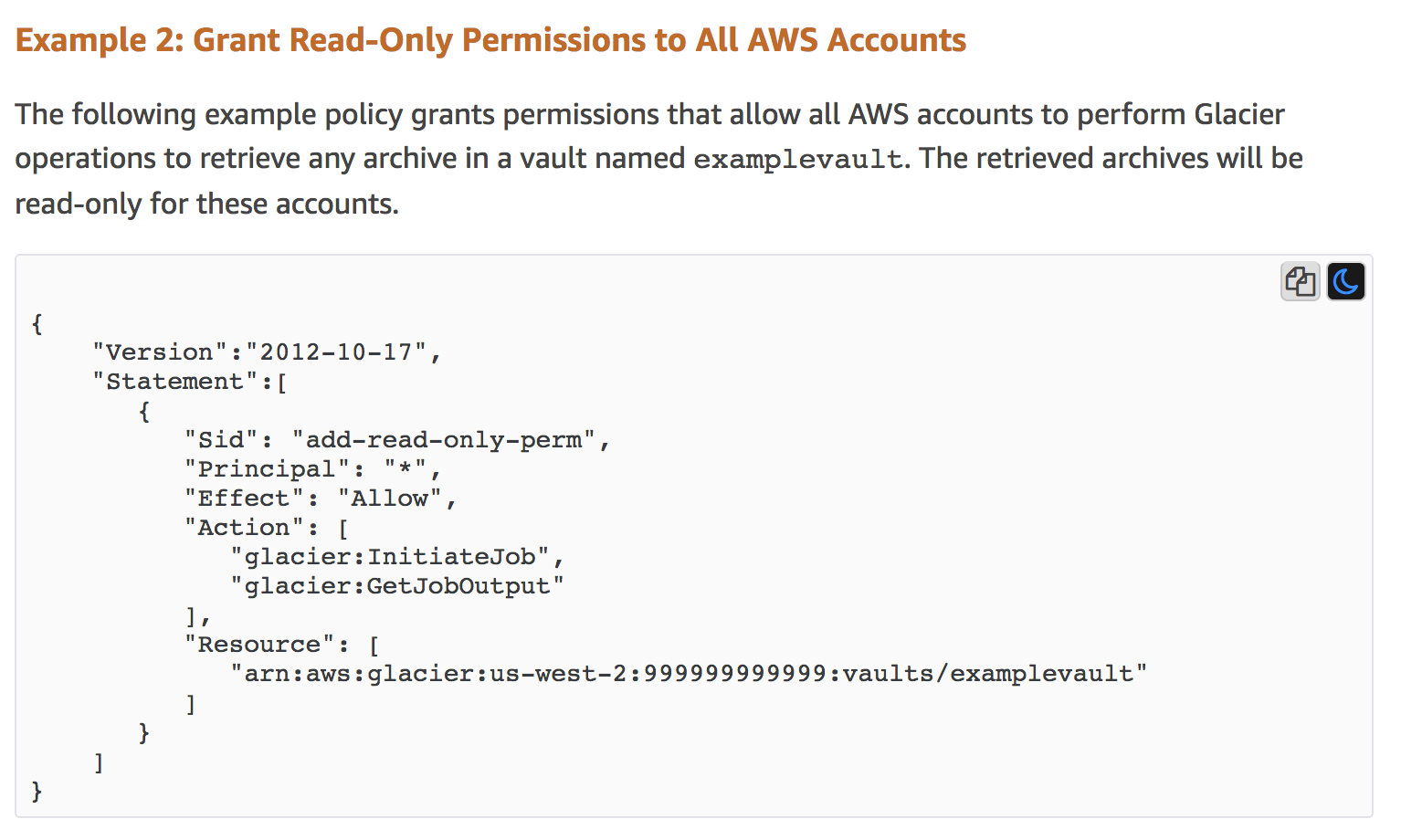
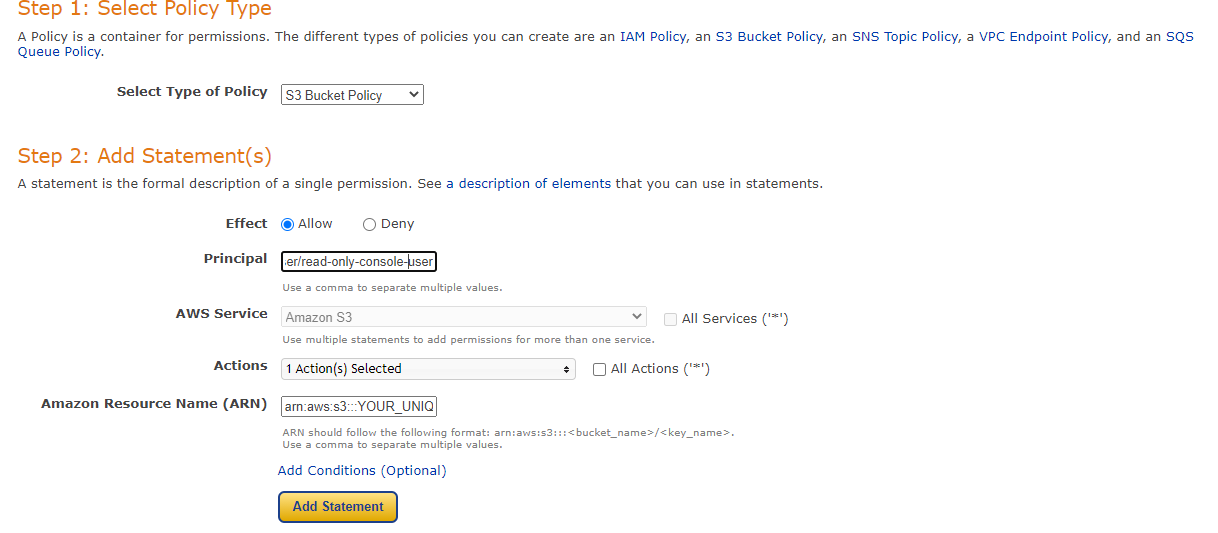
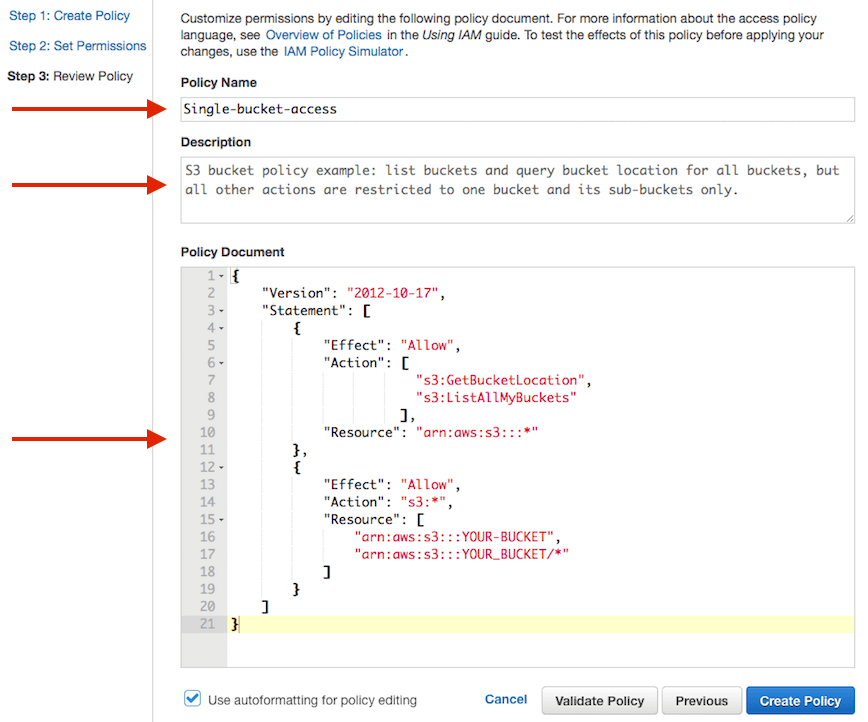
One-Stop IT Service Provider - How exactly to use resource-based policies within the AWS Secrets Supervisor console to securely accessibility secrets across AWS accounts
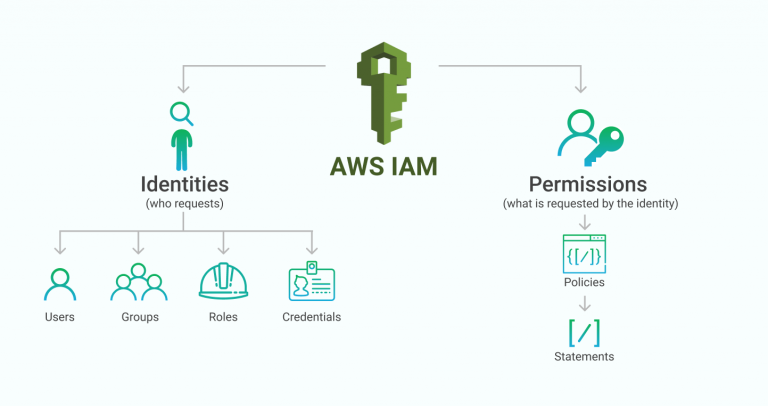
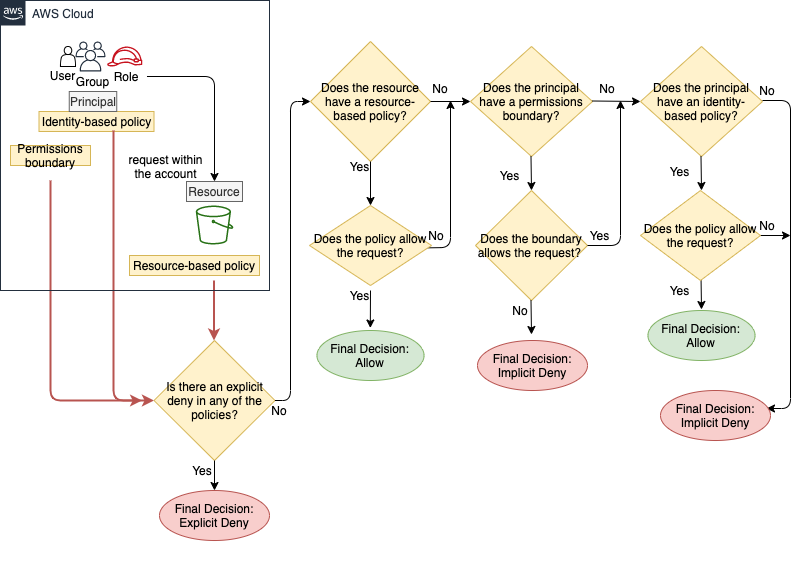
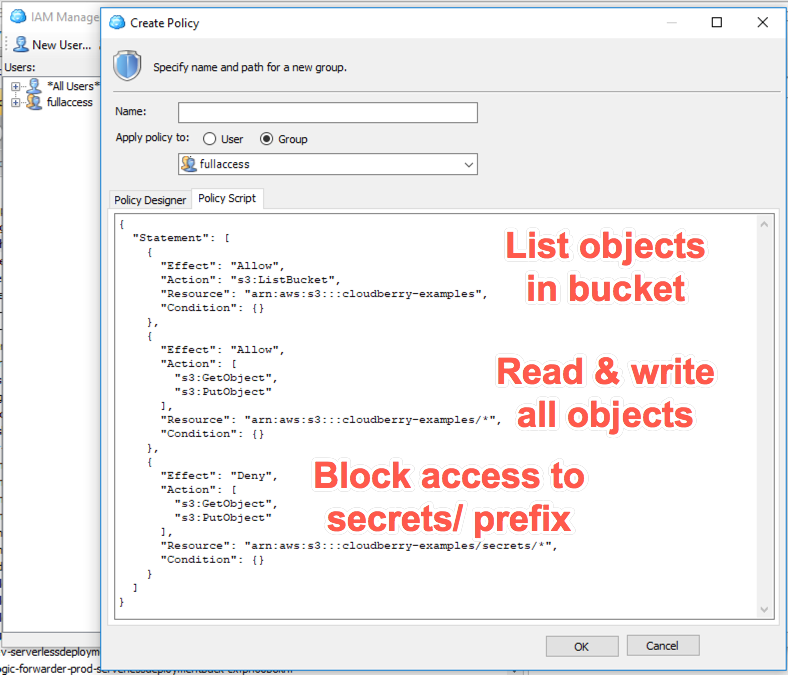
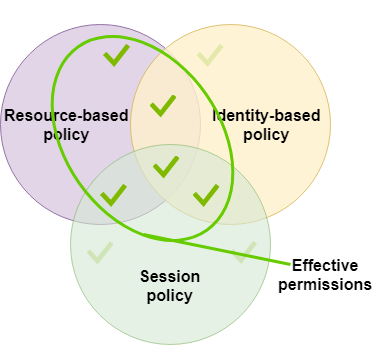
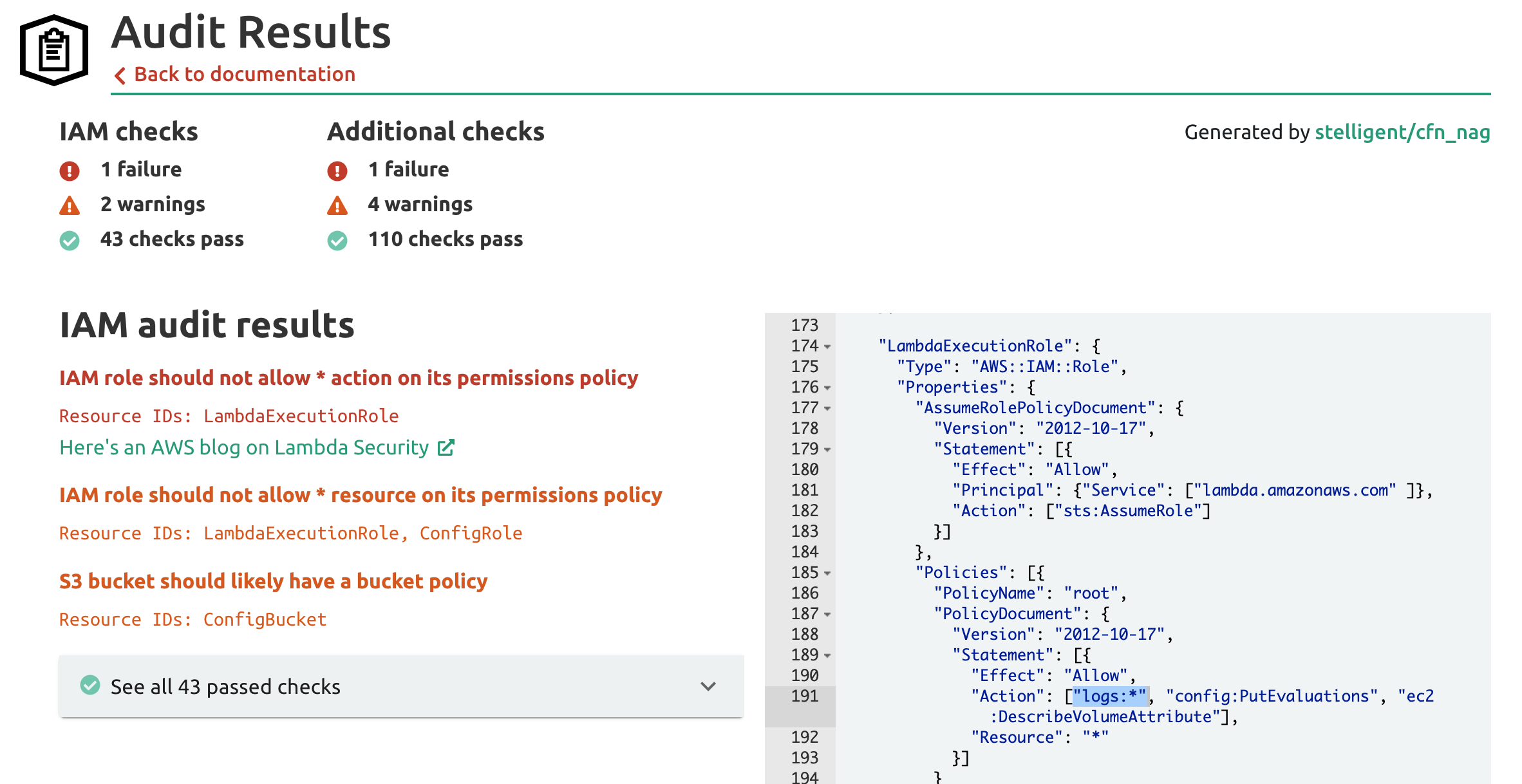
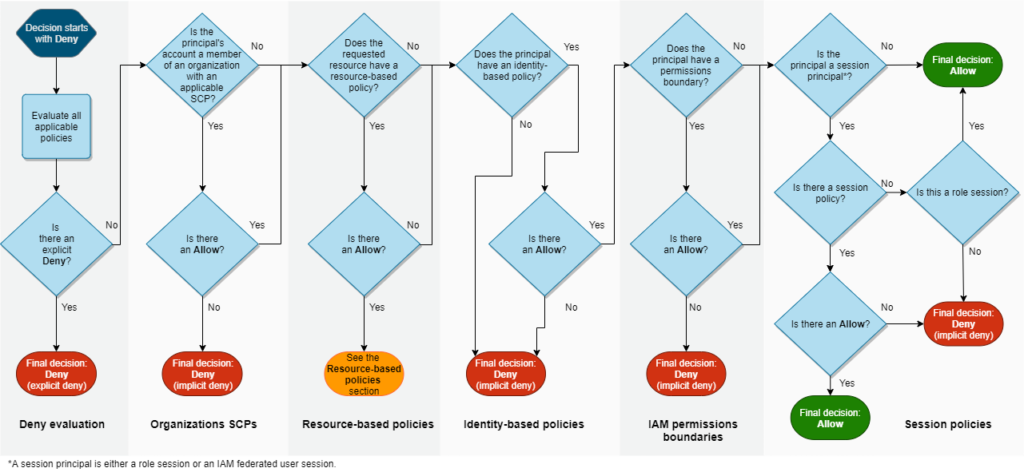
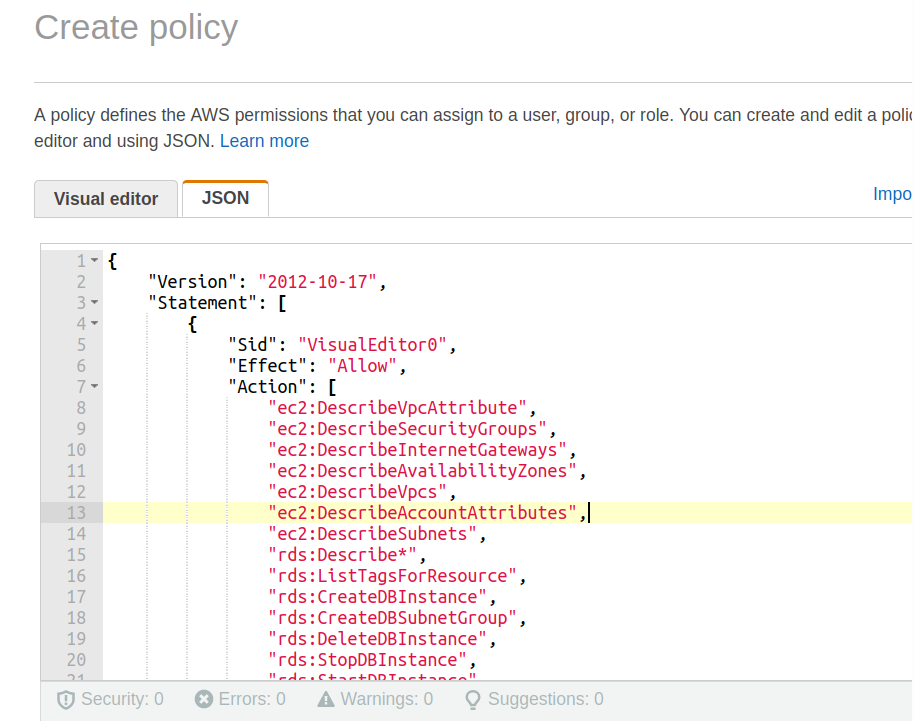
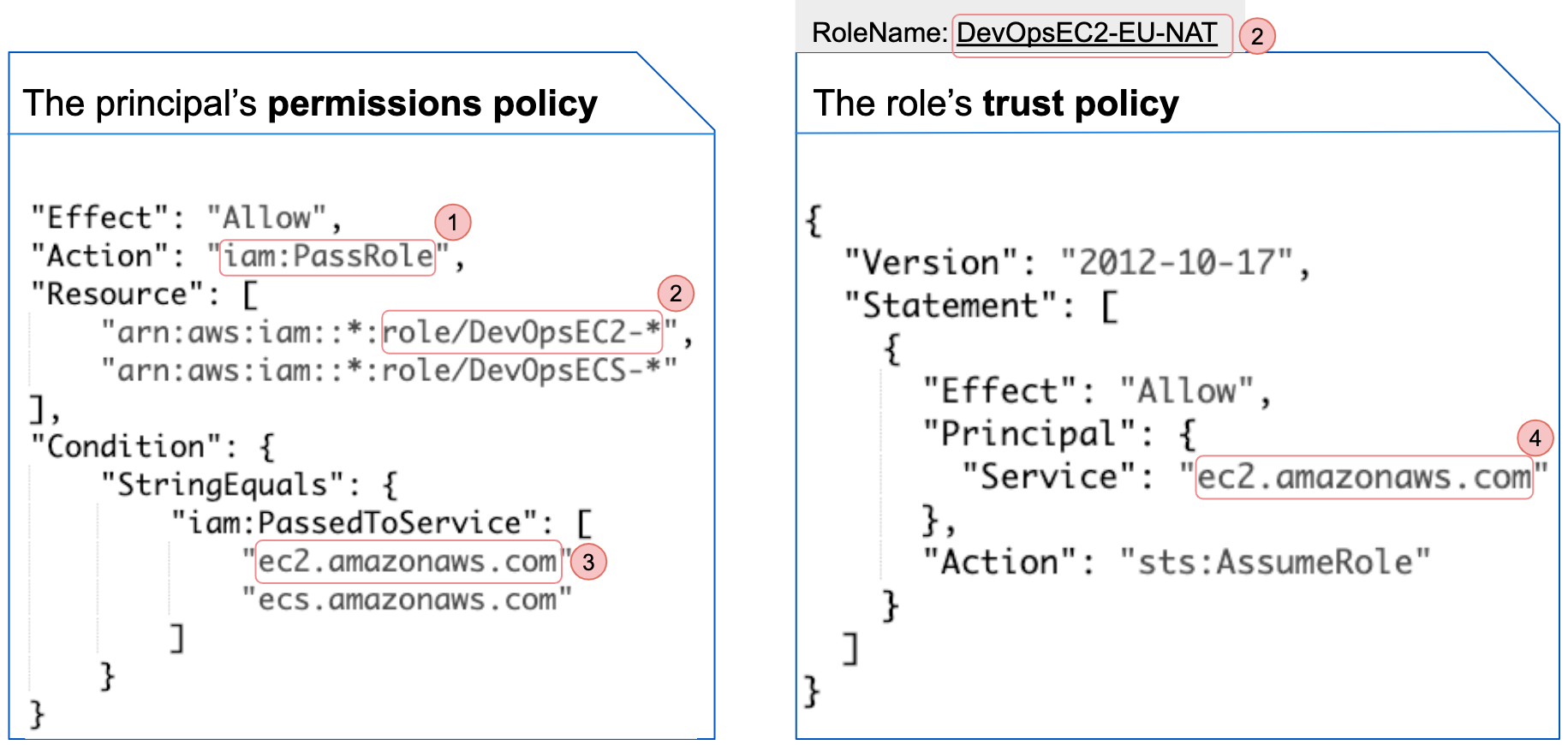
AWS IAM Primer. The 20% of IAM that you need 80% of the… | by George Lutz | Trimble MAPS Engineering Blog | Medium
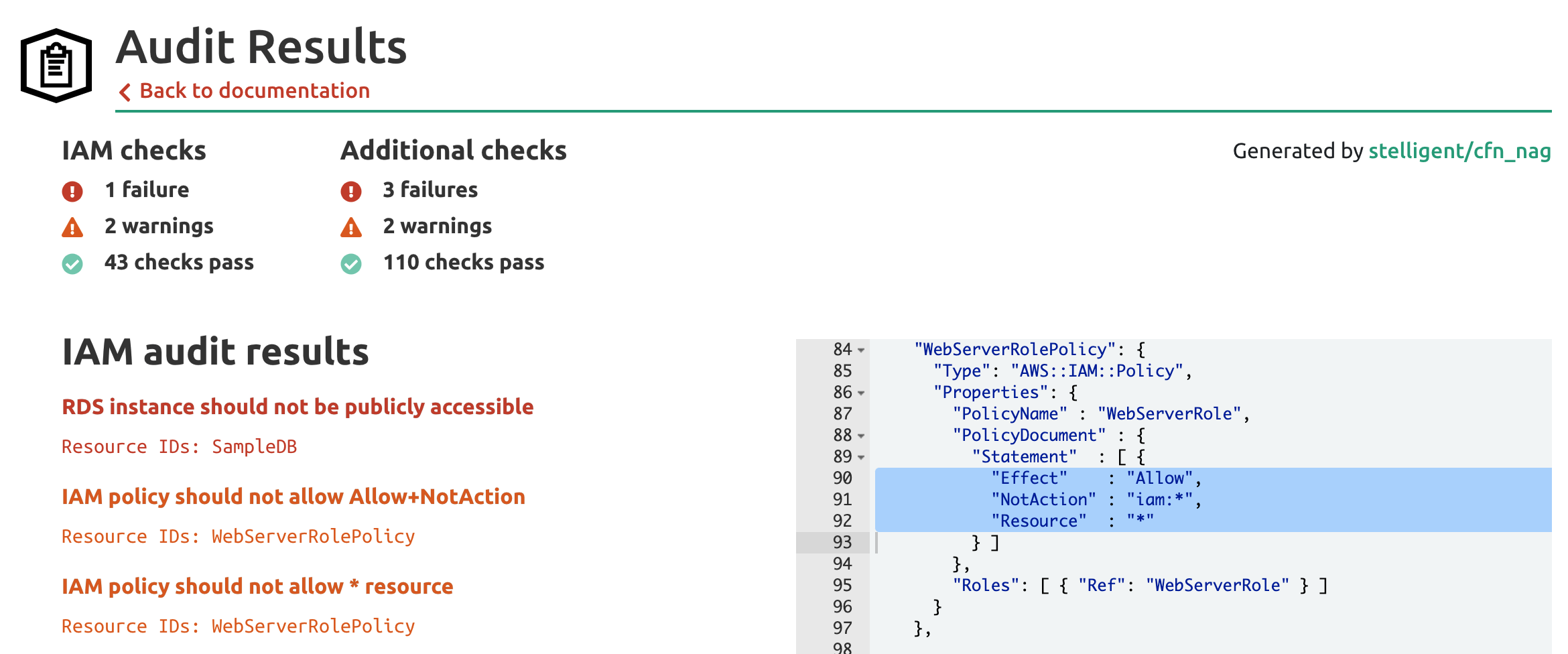
Unit 42 Cloud Threat Report: Misconfigured IAM Roles Lead to Thousands of Compromised Cloud Workloads